Security and Infrastructure
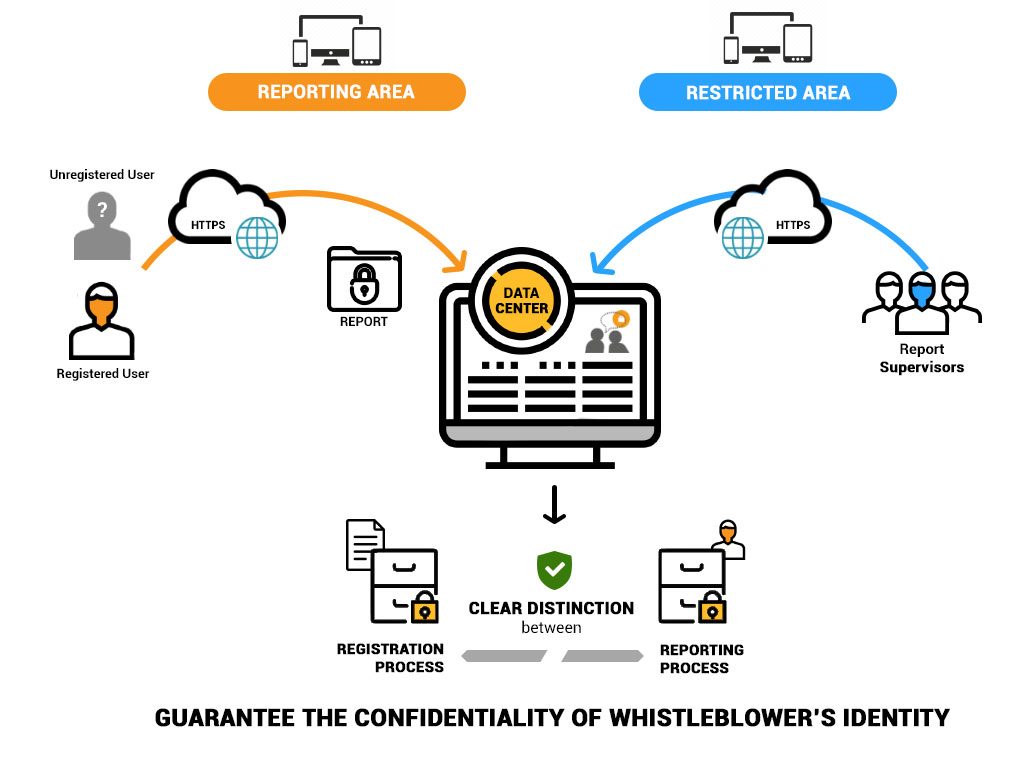
Reports and whistleblowers’ safety
In addition, to protect the identity of the whistleblower and the content of the report:

Software safety and infrastructure
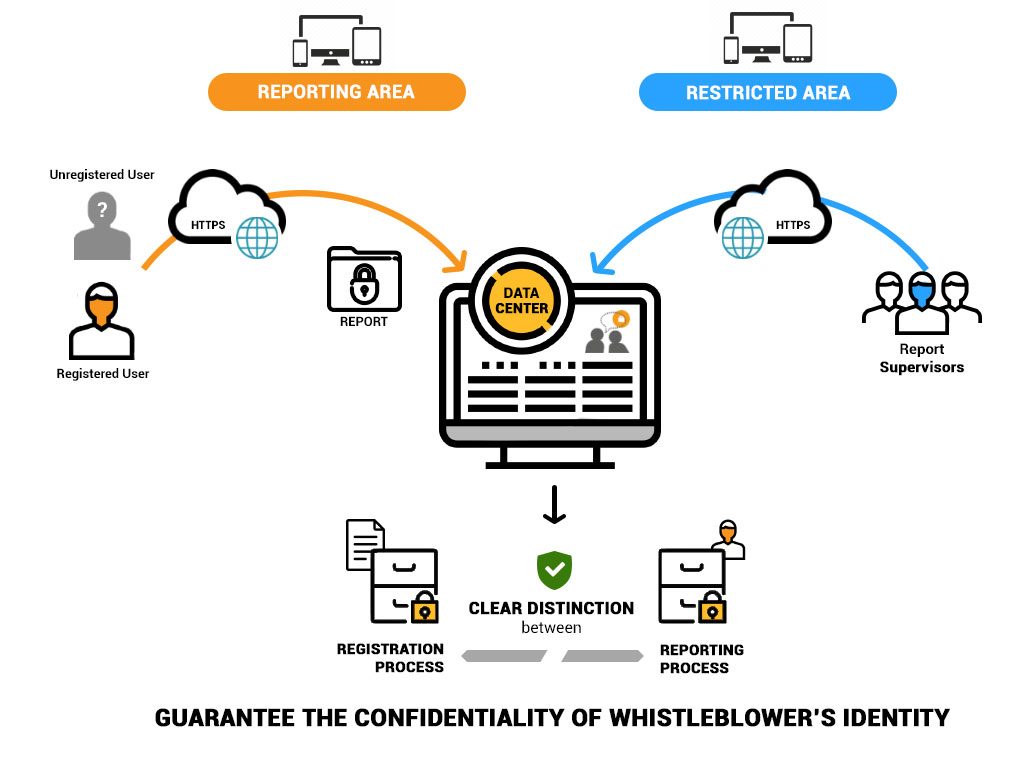
In addition, to protect the identity of the whistleblower and the content of the report: